India’s one of the largest eLearning platforms, Unacademy’s data breach news shook the entire eLearning industry. The security firm, Cyber Inc reported the cyberattack on ed-tech startup’s database which resulted in the exposure of 22 million user details.
The data breach was confirmed by the co-founder and CTO of the online learning platform, Unacademy. In the confirmation statement, Hemesh Singh assured that sensitive information like financial data has not been breached.
The information is up for sale on the dark web and according to some sources has already been sold out! The dark web is pretty much darker than we imagined in our worst nightmares. Hacking intelligence is overpowering our security measures. Time and again, hackers have successfully trespassed the secure boundaries of online companies and left the internet users in utter shock.
This news has been eerily reminiscent of security issues in eLearning platforms. Most of us follow the security checklist during the eLearning platform development. But this time we need to put in all we have within us while following this security checklist stringently.
The Security Challenges in eLearning Website Development
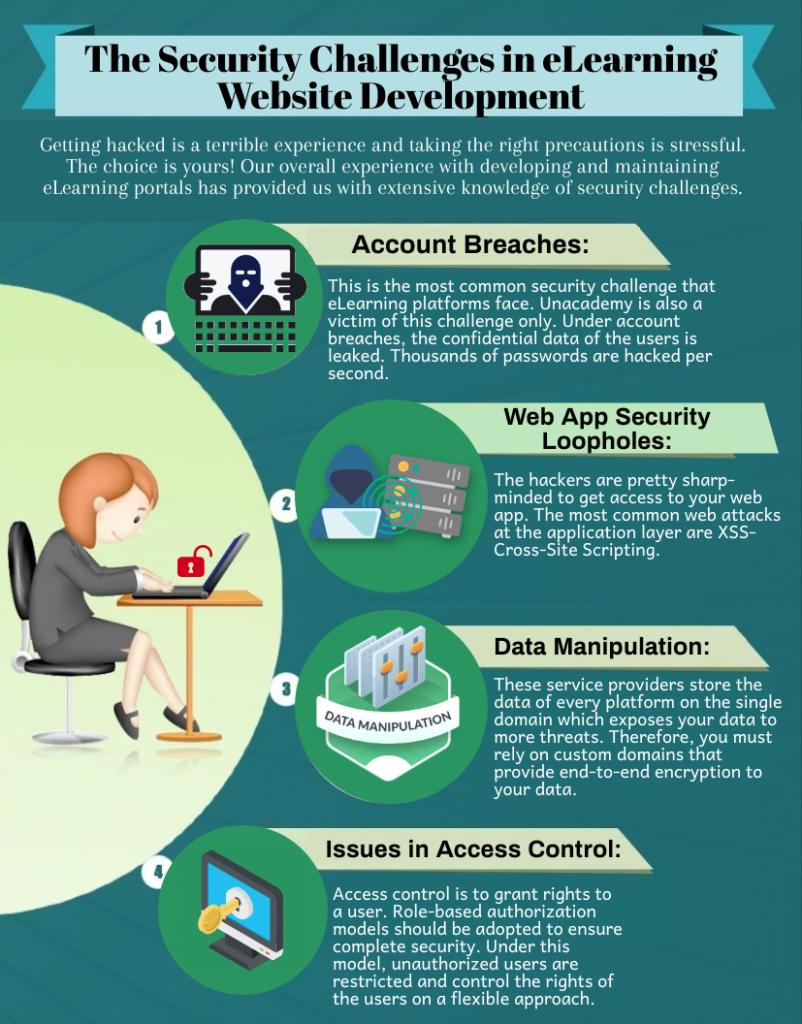
Getting hacked is a terrible experience and taking the right precautions is stressful. The choice is yours! Our overall experience with developing and maintaining eLearning portals has provided us with extensive knowledge of security challenges.
We have prepared this list of the most challenging security concerns that every eLearning platform should beware of to prevent data breaches. Let us talk about every security challenge and the ways to overcome it in detail.
Account Breaches:
This is the most common security challenge that eLearning platforms face. Unacademy is also a victim of this challenge only. Under account breaches, the confidential data of the users is leaked. Thousands of passwords are hacked per second.
This threat is the harsh reality which no business can avoid to face! The dark web is filled with stolen credentials and every day the numbers are increasing. Unacademy might be one of the largest eLearning platforms but organizations like LinkedIn have also been hacked and compromised the information of their users.
Are you wondering about how to overcome this challenge? It’s not very difficult, just ensure that LMS is accessible from the office networks only. This brings in many restrictions but ensures complete security to your database.
Apart from this, choose an LMS with security features like minimum password length, lock account on repeated trials, etc. Make sure to choose an LMS after rigorous inspection and research.
Web App Security Loopholes:
Every web app has security loopholes that have to be identified and resolved before the launch. The hackers are pretty sharp-minded to get access to your web app. The most common web attacks at the application layer are XSS- Cross-Site Scripting. These attacks are on the pages that function on client-side browsers and not on server-side browsers.
Hence, you need to have a stringent checking of front-end coding. HTML and Javascript are the main culprits in this type of web attack. The XSS attacks can alter the browser functionality and result in web app defacement.
The way to prevent such attacks is encrypting the data. Apart from this, do not trust HTTPS websites, provide a clear statement to the database about what is to be expected before any sensitive data is passed on, and a check on users’ inputs can also help immensely.
Data Manipulation:
This is more common in situations when you rely on cloud service. These service providers store the data of every platform on the single domain which exposes your data to more threat. Therefore, you must rely on custom domains that provide end-to-end encryption to your data.
Data encryption is no longer a choice for eLearning platforms. You need to get your data encrypted and take its back-up at regular intervals. Make sure to adhere to the necessary rules and regulations of law.
Issues in Access Control Rules:
Access control is to grant rights to a user. Role-based authorization models should be adopted to ensure complete security. Under this model, unauthorized users are restricted and control the rights of the users on a flexible approach.
This means one user can have more access and another user can have lesser access. Appropriate assignment of roles under this model can successfully deny permission to unauthorized users.
Conclusion:
Apart from checking upon these security threats, it is recommended to ensure your eLearning platform complies with all the related data security laws. There are region-wise data laws like GDPR, Personal Information Protection, and Electronic Documents Act, and the Data Protection Act for EU, Canada, and the UK respectively.
Mind you, precautions are better than regret! One mistake can make you the next news sensation target for a data breach in eLearning platforms. Hence, choose a reliable eLearning website development company that knows the destructive power of a single security loophole. Commit to working with honesty, integrity, and confidentiality.










